So, you've build your own homelab hosted Cloud Foundry environment, but forgot to apply a proper certificate to the gorouter. Let's fix that..
First we need to make a certificate, I'm using self signed here.. good enough for my homelab use-case. The cert needs to have SAN(s) (subject alternative name) and you can only make one with openssl if you use a config file, so here is mine:
ts = 2048
prompt = no
default_md = sha256
x509_extensions = v3_req
distinguished_name = dn
[dn]
C = NL
ST = MyState
L = MyCity
O = MyOrg
emailAddress = email@mydomain.com
CN = *.cf.singel.home
[v3_req]
subjectAltName = @alt_names
[alt_names]
DNS.1 = *.apps.cf.singel.home
DNS.2 = *.system.cf.singel.home
DNS.3 = *.login.system.cf.singel.home
DNS.4 = *.uaa.login.system.cf.singel.home
Issue a:
openssl req -x509 -nodes -days 1365 -newkey rsa:2048 -keyout mycert.key -out mycert.crt -config <your config file here>
Now, paste the contents from the mycert.key and mycert.crt files into your vars.yml like this:
router_tls_pem:
- cert_chain: |
-----BEGIN CERTIFICATE-----
MIIDxzCCAq+gAwIBAgIUHxcEGmmouAbi2WtjQu6QOfbl7eYwDQYJKoZIhvcNAQEL
...
7R9gygDS1oF/dYKVntjeL3vY732vxRzLomw+mv3FpTZ7XWqELRkY8AY1LuOy0vS1
NYiex/DBSWJwMaY=
-----END CERTIFICATE-----
private_key: |
-----BEGIN PRIVATE KEY-----
MIIDxzCCAq+gAwIBAgIUHxcEGmmouAbi2WtjQu6QOfbl7eYwDQYJKoZIhvcNAQEL
...
7R9gygDS1oF/dYKVntjeL3vY732vxRzLomw+mv3FpTZ7XWqELRkY8AY1LuOy0vS1
NYiex/DBSWJwMaY=
-----END PRIVATE KEY-----
And re-run your bosh deployment including
-o cf-deployment/operations/use-operator-provided-router-tls-certificates.yml \
--vars-file ./vars.yml
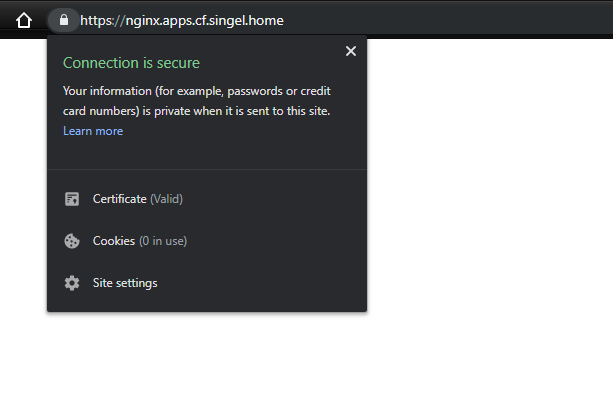
The last step would be importing your cert into the Trusted Root Certification Authorities and presto, you are done: